Configuration du Single Sign-On (SSO)
Vous pouvez accéder à Celoxis avec les identifiants de l'entreprise si le SSO basé sur SAML est activé pour votre compte. Celoxis travaille avec Google, Salesforce, Okta, OneLogin, Microsoft Azure et Microsoft ADFS. Bien que nous n'ayons pas testé, tout IDP basé sur SAML 2.0 devrait fonctionner.
Pour que le SSO fonctionne, il faut s'assurer de ce qui suit :
- Votre fournisseur d'identité SSO (IDP) est basé sur SAML 2.0.
- Tous vos utilisateurs, clients ont une adresse électronique unique.
- L'adresse électronique d'un utilisateur dans Celoxis correspond à l'adresse électronique de cet utilisateur dans votre IDP.
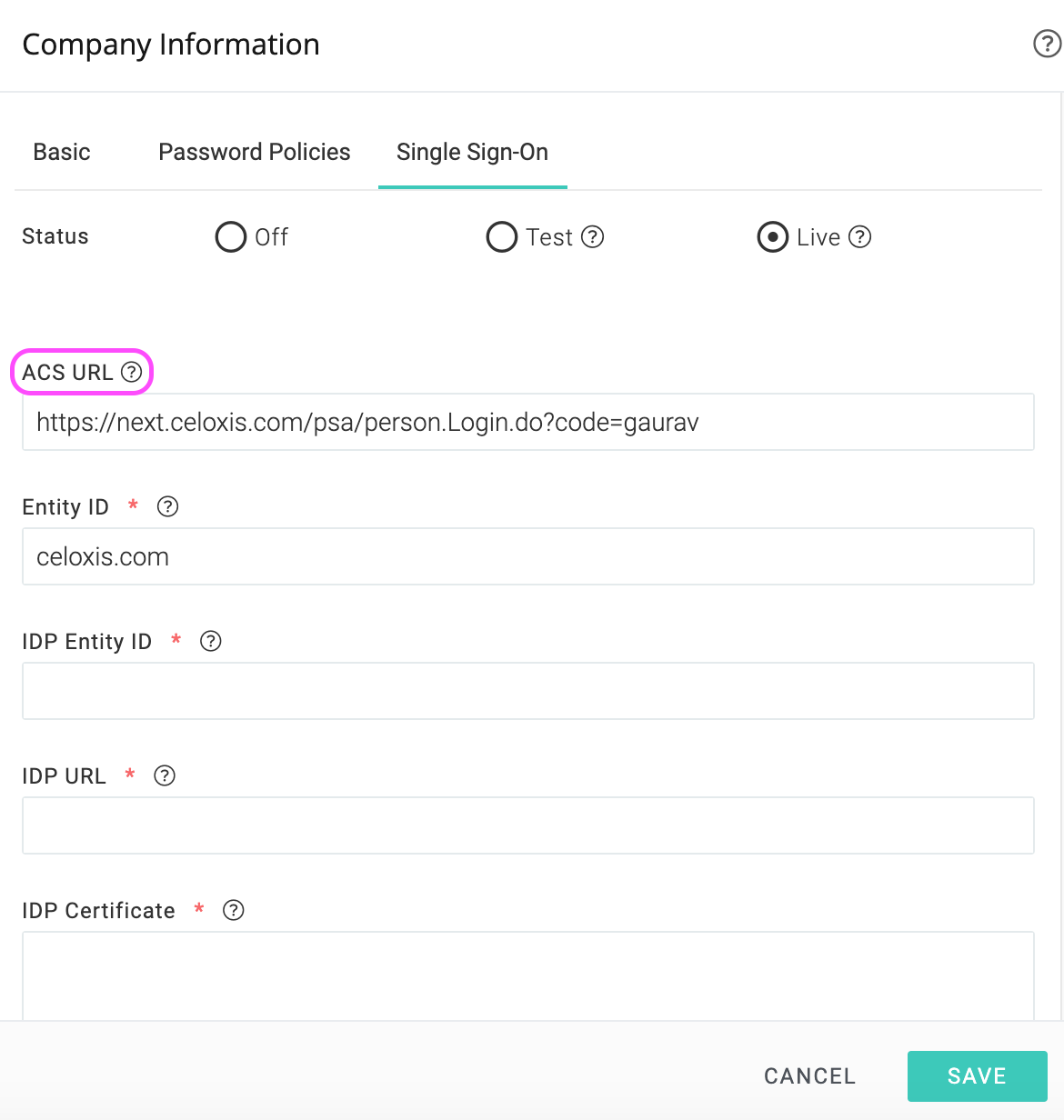
Pour mettre en place le SSO, ouvrez Top Menu ▸ ▸ Admin ▸ AccountManagement ▸ ManageCompany et cliquez sur Inscription unique. Vous verrez le formulaire comme ceci :
Modes SSO
Dans tous les modes, les comptes clients continueront d’être authentifiés à l’aide de Celoxis Pouvoirs.
- Aucun - Le SSO est désactivé. Seuls les informations d'identiifcation de Celoxis peuvent être utilisés pour se connecter.
- Test - Le SSO est activé. Le SSO et les informations d'identification de Celoxis peuvent tous deux être utilisés pour se connecter.
- En direct - Le SSO est en marche. Seul le SSO peut être utilisé pour se connecter.
- Vos utilisateurs ne pourront pas accéder au lien "Mot de passe oublié" en Celoxis car nous ne stockons pas les mots de passe des utilisateurs.
- Vous ne verrez pas les champs Login et Mot de passe sur les formulaires d'ajout/modification d'utilisateur.
- Si vous êtes bloqué pour une raison quelconque, contactez-nous et nous réinitialiserons vos coordonnées SSO.
Étapes de la mise en place d'un SSO
1 : Activer le SSO en mode test
Ouvrez Top Menu ▸ ▸ Admin ▸ AccountManagement ▸ ManageCompany et aller à la Inscription unique onglet
- Dans la ligne État, cliquez sur le bouton radio Tester.
- Dans les options ci-dessous, copiez l'URL ACS. Cela sera nécessaire pour configurer votre IdP (fournisseur d'identité)
- Configurez votre IDP. Le IDP vous donnera un ensemble de paramètres à entrer dans Celoxis.
- Revenez à cet écran avec les paramètres collectés à l'étape précédente.
- Saisissez l'ID de l'entité IDP. Elle est fournie par l'IDP.
- Entrez l’URL du fournisseur d’identité. Il s’agit de l’adresse de votre fournisseur d’identité qui sera contacté pour authentifier les utilisateurs.
- Copier - Coller le certificat IDP. Ces informations sont disponibles dans le certificat fourni par votre IDP
- Cliquez sur "Sauvegarder".
2 : Testez votre installation
- Une fois l'étape 1 terminée, vous devez essayer de vous connecter Celoxisen cliquant sur le lien Connexion via l'identification unique sur la page de connexion.
- Après avoir cliqué sur le lien ci-dessus, vous serez invité à saisir l'adresse électronique.
- Après avoir saisi ce dernier, vous êtes dirigé vers l'écran de connexion de votre IDP ; si vous n'êtes pas encore connecté, vous êtes invité à saisir l'adresse électronique et le mot de passe.
- Une fois l’authentification réussie, vous êtes redirigé vers Celoxis Tableau de bord. Si quelque chose ne va pas, consultez la section Erreurs courantes sous votre fournisseur d’identité.
3 : Allez vivre avec votre SSO
- Une fois l'étape 2 terminée avec succès, vérifiez à nouveau les informations relatives à votre OSP.
- Ensuite, cliquez sur Live.
- Cliquez sur Enregistrer.
Mise en place de votre IDP
Avant d'installer Celoxis, vous devrez d'abord informer votre IDP à propos de Celoxis. Voici les instructions à suivre pour certaines des personnes déplacées les plus populaires. Si votre IDP ne figure pas dans cette liste, veuillez consulter sa documentation.
Toutes les IDPs devront disposer d'une adresse URL ACS pour Celoxis. Vous pouvez le trouver pour votre organisation en cliquant sur les boutons radio Test ou Live comme indiqué ci-dessus.
Créer une application SAML dans Google
- Connectez-vous à votre console d'administration Google à l'aide d'un compte administrateur.
- Cliquez sur Apps > Apps SAML.
- Cliquez sur l'icône "plus" dans le coin inférieur.
- Cliquez sur CONFIGURER MON PROPRE APPAREIL DOUANIER.
- La fenêtre Google IDP Information s'ouvre et l'URL du SSO et les champs d'identification des entités sont automatiquement remplis. Vous devez copier l'ID de l'entité et les valeurs des champs du SSO et télécharger les métadonnées IDP (option 2) pour les coller dans les champs appropriés de Celoxis.
- Une fois que vous avez saisi ces informationsCeloxis, revenez à la console d'administration et cliquez sur Suivant.
- Dans le
Fenêtre de base, entrez un nom et une description de la demande. - Cliquez sur Suivant.
- Dans la fenêtre "Détails du fournisseur de services", entrez :
- URL ACS : Entrez la valeur copiée à partir de l'onglet SSO.
- Identification de l'entité: Entrez Celoxis.com
- Démarrer l'URL: Pour le SaaS, entrez https://app.celoxis.com/psa/person.Login.dopour le service Sur Site, https://your_URL/person.Login.do
- Ne pas cocher la case Réponse signée.
- Sous l'ID du nom, pour les informations de base, sélectionnez l'adresse électronique principale.
- Dans la liste déroulante Format d'identification du nom, choisissez EMAIL.
- Cliquez sur Suivant.
- Cliquez sur Terminer.
Activer l'application SAML pour les utilisateurs
- Allez à Apps > Apps SAML.
- Sélectionnez l'application SAML que vous avez créée ci-dessus.
- En haut de la boîte grise, cliquez sur Paramètres et choisissez Activé pour tous et confirmez les paramètres.
Erreurs courantes
Erreur : app_not_enabled_for_user
Solution : Vous n'avez pas activé l'application SAML pour vos utilisateurs. Suivez les étapes mentionnées ci-dessus pour activer l'application pour tout le monde. La même erreur s'affiche si vous êtes connecté à un compte Google en utilisant un utilisateur différent de celui configuré pour l'IDP.
Erreur de serveur : Aucune société trouvée avec le code de la société : XXXX
Solution : L'URL ACS que vous avez saisie dans la configuration de Google est incorrecte. Copiez l'URL correcte à partir du champ URL de l'AEC sous l'onglet Single Sign-On dans Celoxis.
Demande invalide, pas d'idpId dans l'URL de la demande ou dans le paramètre de destination de la demande SAML.
Solution : L'URL du IDP que vous avez entré dans Celoxis est incorrect. Vous devez copier ceci de votre IDP et le coller dans Celoxis.
- Activer mon domaine à partir de l'installation > Administrer > Gestion des domaines > Mon domaine. Déployez-le pour tous les utilisateurs. Cela créera automatiquement le fournisseur d'identité Salesforce.
- Naviguez jusqu'à Administrer > Contrôles de sécurité > Fournisseur d'identité. Vous verrez les détails de configuration du fournisseur d'identité qui doivent être saisis dans Celoxis.
- Cliquez sur le bouton "Télécharger les métadonnées" pour télécharger le certificat. Le contenu de ce certificat doit être saisi dans le champ IDP Certficate Celoxiscomme décrit précédemment dans le document.
- Maintenant, sur la même page ci-dessous, cliquez sur Les fournisseurs de services sont maintenant créés via les applications connectées. Cliquez ici.
-
Sur la Nouvelle application connectée entrez les informations suivantes :
- Nom de l'application connectée
- Démarrer l'URL
- Cochez la case Activer SAML.
- Identification de l'entité
- URL DE L'AEC
- Type de sujet : Sélectionner un attribut personnalisé
- Format de l'identifiant du nom: Sélectionnez urn:oasis:names:tc:SAML:1.1:nameid-format:emailAddress
- Certificat IdP : Sélectionnez le certificat approprié dans lequel vous êtes entré (étape Celoxis3)
- Cliquez sur Enregistrer.
- Après la création de l'application, vous devez maintenant y associer des profils d'utilisateurs afin que les utilisateurs appartenant à ces profils puissent se connecter via le SSO.
Naviguer vers Gérer les applications > Applications connectées. Cliquez sur l'application que vous venez de créer. - Faites défiler vers le bas et cliquez sur Gérer les profils.
- Sélectionnez les profils requis et cliquez sur Enregistrer.
Erreurs courantes
Erreur de serveur non authentifié
Solution : Le certificat IDP que vous avez saisi Celoxisest incorrect. Saisissez le certificat correct que vous avez créé pour cela (étape 3 ci-dessus)
Vous serez confronté à la même erreur si vous n'avez pas associé le profil de l'utilisateur qui se connecte à l'application Connected comme expliqué aux étapes 7 à 9 ci-dessus.
- Connectez-vous à votre organisation Okta en tant qu'utilisateur disposant de privilèges administratifs.
- Cliquez sur le bouton Admin en haut à droite.
- Cliquez sur l'étiquette "Add Apps".
- Cliquez sur le bouton Créer une nouvelle application.
- Dans la boîte de dialogue qui s'ouvre, sélectionnez l'option SAML 2.0, puis cliquez sur le bouton Créer.
- Sur la page Paramètres généraux, entrez le nom de l'application, par exemple Celoxisdans le champ Nom de l'application, puis cliquez sur le bouton Suivant.
- Pour Configurer SAML à l'étape, entrez les informations suivantes :
- Signe unique sur l'URL : Voici l'URL de l'AEC que vous recevrez de Celoxis
- URI du public (ID de l'entité SP): Pour les utilisateurs de SaaS, entrez : https://app.celoxis.comPour les utilisateurs sur site, entrez l'URL de votre application.
- Format de l'identifiant du nom: Adresse électronique
- Cliquez sur Suivant.
- Dans Feedback, sélectionnez "I'm an Okta customer adding an internal app", et "This is an internal app that we have created", puis cliquez sur Finish.
- Dans la section "Personnes" de la demande, cliquez sur le bouton "Assigner à des personnes". Sélectionnez les utilisateurs requis et cliquez sur Terminé.
- Dans la section "Sign On" de votre nouvelle application, cliquez sur "View Setup Instructions". Un nouvel onglet s'ouvre avec les détails que vous devez entrer dans Celoxis. Remplissez l'onglet "Single Sign-On" dans Celoxis comme mentionné précédemment dans ce document.
Erreurs courantes
Si vous êtes toujours invité à fournir des informations d'identification après avoir cliqué sur Connexion via le SSO et avoir saisi les informations d'identification du SSO, cela signifie que vous avez saisi l'URL de l'AEC /Single sign on URL dans Okta de manière incorrecte. Veuillez corriger et réessayer.
Sorry, you can't access <app name> because you are not assigned this app in Okta.
The user who is trying to login via SSO is not assigned to the app created in Okta. Redo the step Assign to People mentioned above.
- Connectez-vous à votre compte OneLogin avec des privilèges d'administrateur.
- Cliquez sur Demandes > Demandes dans le menu principal.
- Cliquez sur le bouton Ajouter une application.
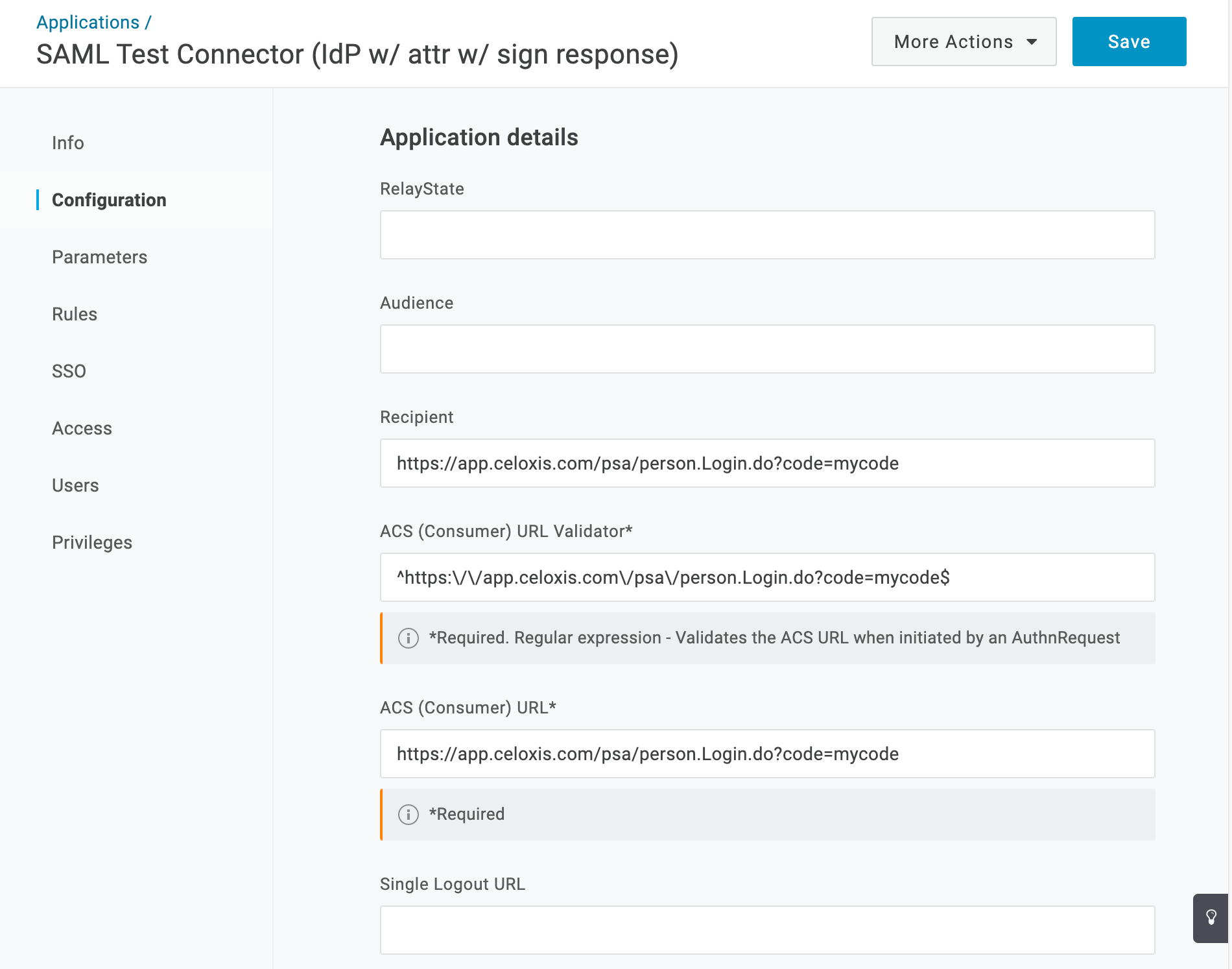
- Recherchez le connecteur de test SAML (IdP avec attr avec signe de réponse) et cliquez dessus.
- Entrez Celoxis comme nom d'affichage et cliquez sur Enregistrer.
- Cliquez sur l'onglet Configuration.
- Copiez l'URL de l'ACL Celoxisdans l'onglet URL du destinataire et de l'ACS (consommateur).
- Dans le Champ du validateur d'URL ACS (consommateur), échappez à l'URL ACS comme indiqué dans la documentation OneLogin. En bref, vous devez préfixer l'URL par ^ mettre le caractère backslash (\) avant chaque caractère de barre oblique. ^https:\/\/app.Celoxis.com\/psa\/personne.Login.do?code=abc
- Votre écran OneLogin devrait ressembler à ceci : Cliquez sur le Sauvegarder bouton.
- Cliquez sur l'onglet SSO.
- Copiez l'URL du point final SAML 2.0 (HTTP) et définissez le comme l'URL IDP dans Celoxis.
Erreurs courantes
The response was received at <Celoxis URL> instead of <URL>
The ACS (Consumer) URL Validator is not URL escaped as shown in screenshot above.
- Connectez-vous au serveur ADFS.
- Lancez la console de gestion ADFS.
- Ouvrez le dossier AD FS > Relations de confiance dans le menu LHS.
- Cliquez avec le bouton droit sur "Replying Party Trusts" et choisissez l'élément de menu "Add Relying Party Trust...".
- Cela ouvrira un magicien. Cliquez sur le bouton Démarrer.
- Dans l'étape Sélectionner la source de données, sélectionnez l'option Saisir manuellement les données sur la partie qui se fie à la demande. Cliquez sur Suivant.
- Dans l'étape Préciser le nom d'affichage, entrez Celoxis. Cliquez sur Suivant.
- Dans l'étape Choisir un profil, sélectionnez le profil AD FS. Cliquez sur Suivant.
- Dans l'étape de configuration du certificat, nous utiliserons les valeurs par défaut. Cliquez sur Suivant.
- Dans l'étape Configurer l'URL, cochez l'option Activer la prise en charge du protocole SAML 2.0 WebSSO. Sous l'URL du service SSO SAML 2.0 de la partie relais, entrez l'URL ACS copiée de Celoxis. Cliquez sur Suivant.
- À l'étape Configuration des identificateurs, entrez l'URL de l'AEC comme identificateur de confiance de la partie relais et cliquez sur Ajouter. Cliquez sur Suivant.
- Dans l'étape Configurer le multi-facteur..., nous utiliserons les valeurs par défaut. Cliquez sur Suivant.
- À l'étape Choisir l'autorisation de délivrance..., choisissez Autoriser tous les utilisateurs à accéder à cette partie dépendante. Cliquez sur Suivant.
- Dans l'étape Prêt à ajouter de la confiance, un aperçu de vos paramètres vous sera présenté. Cliquez sur Suivant.
- À l'étape Terminer, sélectionnez l'option Ouvrir les revendications de modification... Cliquez sur Fermer.
- La fenêtre de l'éditeur de réclamations devrait maintenant s'afficher.
- Cliquez sur Add Rule... sous l'onglet Issuance Transform Rules.
- Dans l'étape Choisir le type de règle, sélectionnez Envoyer les attributs LDAP en tant que réclamations comme modèle de règle de réclamation . Cliquez sur Suivant.
- Sur l'écran suivant, en utilisant Active Directory comme magasin d'attributs, faites ce qui suit :
- Dans la colonne Attributs LDAP, sélectionnez Adresses électroniques.
- Dans le Type de demande de remboursement sortant, sélectionnez Adresse électronique.
- Cliquez sur OK pour enregistrer cette règle.
- Cliquez sur Add Rule... sous l'onglet Issuance Transform Rules pour ajouter une nouvelle règle.
- Dans l'étape Choisir le type de règle, sélectionnez Transformer une demande entrante comme modèle de règle de réclamation . Cliquez sur Suivant.
- Sur l'écran suivant :
- Sélectionnez Adresses E-Mail comme type de demande entrante.
- Sélectionnez Nom ID comme type de demande sortante.
- Sélectionnez EMail comme format d'identification du nom sortant.
- Sélectionnez l'option Passer par toutes les valeurs de réclamation.
- Cliquez sur OK pour enregistrer cette règle.
- Cliquez sur OK pour terminer la création des règles.
Nous allons maintenant exporter le certificat qui doit être copié vers Celoxis
- Ouvrez le dossier AD FS > Settings > Certficates dans le menu LHS. Le volet Certificats affichant tous les certificats disponibles apparaît.
- Sélectionnez le certificat sous Signature de jeton dans le volet Certificats.
- Cliquez sur l'option Copier dans le fichier dans l'onglet Détails de la fenêtre du certificat. Cela lance l'assistant d'exportation de certificat.
- Dans l'étape Bienvenue, cliquez sur Suivant.
- Choisissez Base64 encodé X.509 (.CER) comme format de fichier dans lequel le certificat doit être exporté. Cliquez sur Suivant.
- Enregistrez le fichier à un endroit approprié et complétez l'assistant.
- Assurez-vous que le fichier sauvegardé a le .CER extension.
- Vous devrez copier-coller le contenu de ce fichier dans le champ "IDP Certficate" Celoxiscomme décrit précédemment dans ce document.
- Connectez-vous au portail Azure.
- Dans le menu LHS, cliquez sur Azure Active Directory.
- Dans le menu Azure Active Directory, cliquez sur Enterprise applications.
- Cliquez sur Nouvelle application en haut de l'écran.
- Dans la section Ajouter une candidature, choisissez Candidature hors galerie.
- Donnez un nom à la nouvelle demande (par exemple CeloxisSSO) et cliquez ensuite sur Ajouter en bas de l'écran. Cela ajoutera une application personnalisée à votre Azure Active Directory. Note : Si vous n'avez pas activé Azure AD Premium, vous ne pourrez pas entrer le nom de l'application.
- Sur la page de candidature, cliquez sur Utilisateurs et groupes dans le menu LHS.
- Dans le volet de droite de la page d'accueil, cliquez sur Ajouter un utilisateur pour affecter des utilisateurs ou des groupes à cette application.
- Cliquez sur Single sign-on dans le menu LHS et choisissez ensuite SAML comme méthode de connexion unique.
- Cliquez sur le à côté du titre de la Configuration de base du SAML et entrez les détails comme suit :
- Identificateur (Entity ID) : Entrez la valeur dans l'onglet Single Sign-On (voir l'image ci-dessus).
- URL de réponse (URL du service aux consommateurs) : Copiez les détails de sous le champ URL du SAC (Admin > Paramètres de l'entreprise)
- S'inscrire sur l'URL : Pour le SaaS, entrez https://app.celoxis.com. Pour On-Premise, entrez votre URL.
- État relais : Sauter ce champ
- URL de déconnexion : Pour le SaaS, entrez https://app.celoxis.com/psa/logout.do. Pour le service Sur Site, entrez [your-url]/psa/logout.do
- Retournez à l'écran de configuration.
- Cliquez sur l'icône située à côté du titre du panneau "Attributs de l'utilisateur et revendications".
- Cliquez sur l'icône située à côté de la valeur de l'identifiant du nom. Une barre latérale Gérer les réclamations des utilisateurs apparaîtra.
- Entrez un nom et sélectionnez user.mail dans le Attribut de la source liste déroulante. Cliquez sur Sauvegarder.
- Retournez à l'écran de configuration.
- Cliquez sur l'icône située à côté du titre du panneau du certificat de signature SAML.
- Entrez un courriel de notification pour les rappels d'expiration des certificats. Cliquez sur Enregistrer.
- Retournez à l'écran de configuration.
- Cliquez sur Télécharger à côté de l'option Certificat (Base64) pour enregistrer le fichier de certificat sur votre ordinateur. Vous devez le copier-coller Celoxiscomme décrit plus haut dans ce document.
- Retournez à l'écran de configuration.
- Cliquez sur Valider pour valider la signature unique avec Celoxis.